Pol88 isn't just a simple player in the digital world. He wields himself with an aura of enigma, always several leagues ahead of the competition. His maneuvers are shrouded in mystery, leaving his opponents baffled. Pol88 is a master craftsman of deception, crafting narratives that mislead. He exploits vulnerabilities with delicate finesse, leaving a trail of frustration in his footprints.
Pol88: An Exploration of Modern Digital Conflict
In the shadowy realm of cybersecurity/digital warfare/online conflict, a new threat has emerged, one that operates in the silent world of bits and bytes/code and algorithms/electronic signals. This is the domain of Pol88, a prolific/notorious/influential group allegedly/reportedly/supposedly engaged in high-level/sophisticated/advanced cyber attacks/operations/campaigns that target critical infrastructure/government agencies/financial institutions. Their motives are shrouded in mystery/secrecy/obscurity, but the scale/scope/impact of their operations is undeniable.
Experts/Analysts/Researchers are racing to uncover/decipher/understand Pol88's tactics, tools, and infrastructure/network/operations. The group's modus operandi often involves zero-day exploits/stealthy intrusions/targeted phishing campaigns, leaving behind a trail of disruption/damage/chaos.
- Governments/Security Agencies/International Organizations worldwide are heightening security measures/implementing countermeasures/launching investigations in an effort to combat this growing threat.
- The question remains: can we stay one step ahead of Pol88 and protect our increasingly connected/vulnerable/digital world?
Unmasking Pol88: Anatomy of a Cyber Threat
Pol88 has emerged as a malicious threat actor, orchestrating sophisticated cyberattacks across multiple industries. This widespread campaign showcases Pol88's sophisticated capabilities and its relentless pursuit of sensitive information.
Analysts are currently dissecting the inner workings of this threat actor, revealing their tactics, techniques, and procedures (TTPs) to appropriately counter their actions.
Pol88's modus operandi often utilizes a multi-stage approach, initiating with surveillance. They then harness vulnerabilities to penetrate target systems, ultimately exfiltrating valuable data.
Measures are underway to mitigate the Pol88 threat. Security researchers work in tandem to formulate effective countermeasures, educate organizations about the latest threats, and enhance cybersecurity defenses.
Pol88's Cybersecurity Effects
The emergence of this novel threat actor Pol88 has sent ripples through the cybersecurity community. Their sophisticated methods have been observed targeting a range of sectors, raising concerns about their potential for widespread impact. Researchers are actively working to analyze Pol88's motives and capabilities, while organizations implement enhanced security measures to counter the risk of compromise.
The sophistication of Pol88's operations emphasizes the need for continuous proactive measures in the cybersecurity landscape. Sharing of threat intelligence and best practices is crucial to effectively combating this emerging threat.
Fighting Back Against Pol88: Strategies and Solutions
Pol88 is a dangerous threat that can wreak havoc on your systems. Battling it get more info effectively requires a multi-faceted approach. First, it's crucial to deploy robust defenses on all your machines. This includes firewalls and regularly updating your software.
Furthermore, educating users about Pol88 and its tactics is essential. Emphasize the significance of being cautious with emails and avoiding questionable sources. Fostering a culture of cybersecurity awareness can significantly reduce your vulnerability.
Should you encounter a Pol88 infection, it's imperative to take immediate measures. Isolate the affected network and seek expert support for remediation.
Remember, proactive defense is your best weapon against Pol88.
Pol88 Attacks: A Constantly Changing Threat
The threat landscape surrounding Pol88 attacks is rapidly shifting. Attackers are constantly exploiting new vulnerabilities and tactics to compromise systems. This ongoing evolution presents a significant challenge for security experts, who must remain vigilant and responsive in their efforts to address these threats.
Furthermore, the complexity of Pol88 attacks is escalating. Attackers are now employing complex techniques, such as automation, to perform attacks more rapidly. This trend emphasizes the urgent need for robust security strategies to stay ahead of these evolving threats.
- Security researchers are actively working to uncover new vulnerabilities and develop effective countermeasures against Pol88 attacks.
- Businesses must prioritize security awareness training and implement strong security policies and procedures to reduce their risk of becoming victims.
 Anna Chlumsky Then & Now!
Anna Chlumsky Then & Now!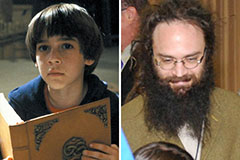 Barret Oliver Then & Now!
Barret Oliver Then & Now! Jonathan Lipnicki Then & Now!
Jonathan Lipnicki Then & Now! Yasmine Bleeth Then & Now!
Yasmine Bleeth Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now!